About
It’s not just about ADS, there is more.
Libre Malware Problem:
A fairly recent way of disguising malware is to distribute it as Free Software and/or privacy oriented. Maybe the source code does not contain spyware and trackware, but the compiled version does. Icecat is regularly tested for unwanted connections coming from upstream Firefox source code. The source code of Firefox is just huge to say the least and it cannot be check by hand. So, I recently came up with a couple of ways for doing this, the best so far is using network namespaces and wireshark. You can read more on this topic here: https://blog.icecatbrowser.org/blog/20231221/application-network-auditing/
The Phone-Home problem:
A fresh installed Firefox, as soon as it is started, connects by default to several services owned by Mozilla (Telemetry) with so called “pings”, in the background and without asking for user permission*, signaling Mozilla and all the parties involved in the connection, that the user just open the browser. This antisocial and debatable behavior is consolidated among all major browsers developers and software vendors in general.[1]
Icecat mitigates this by:
– Removing Telemetry at compile time.
– Disabling checks for updates (you have to check for
updates yourself).
– Disabling DRM
Differently from the many Firefox Forks out there, Icecat is the only one that doesn’t send out any data, unless the user decides.
The ‘Third Parties’ problem
When we open a web url, our browser will download a web page (html) and
all the referenced javascript, images, css etc.
The problem is that
many of these are often downloaded from third parties servers, who in
turn, can log our visit, see our ip address, fingerprint our browser,
and even worse, try execute some dangerous javascript. The majority of
the browsers will happily execute any javascripts for the sake of the
web, otherwise some website might not look as expected or might not have
certain functionalities.
Some of these resources are
included in a webpage with the only purpose of logging and
tracking the user activity.
Think of Google
Analytics: it’s almost everywhere and while the one website
owners, can use analytics to get some stats about the website visitors,
Google, on the other hand, can see the activity of all the users across
many websites (the majority use Google Analytics) and build complete
user profiles in an illegal and unethical way: without user consent,
without letting the users know and with no chance of
opting-out.
This also tells us why Google Analytics
is GRATIS… Or is it?.
Icecat tries to mitigate this with the following
settings:
– Isolate requests to First Party domains
– Do not load custom fonts
– Spoof Referers
– Resist Fingerprinting
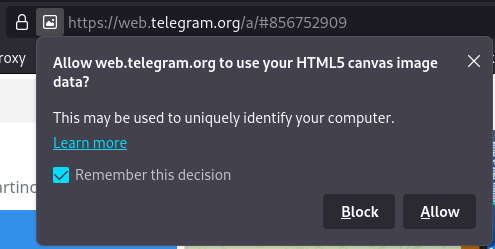
– Prevent HTML5 Canvas data as default
– Prevent execution of Javascripts without a proper
License (LibreJS)
– Prevent the execution of potentially dangerous
javascript
The Big Picture (spoiler: it’s bad)
In normal circumstances and using the default settings of most of the
modern browsers, our connections go through network devices (routers)
that belong to unknown third parties, our browser needs to use services
like DNS, so, for these reasons, our activity leaves traces behind.
These traces are meticulously collected on different levels by different
actors and built up over time (think years of tracking). This data is
collected from several sources: for example, from Mastercard (all your
purchases, yes, they do sell your data [2]), Facebook (Location,
friends, gender, age, relationship graph [3]) , Whatsapp (same as
facebook, plus address book), your mobile phone ISP (real approximate
location 24h/D), some other data brokers and put everything
together.
At this point we have a glimpse into the big picture and
can confidently say that there is someone out there who knows me, my
habits, my taste in music, my political views, my loving preferences, my
readings and my purchases very well; probably better than I do.
Unfortunately this has horrible and damaging consequences on a
collective level, where anyone sufficiently financed can buy and abuse
these information in a number of different ways and we are not going to
list them because, for how good the list could be, it would always be
only a part of what actually happens out there, out of sight.
By using Icecat, I hope, we can change this consolidated behavior by making the data unavailable for collection, at least from the desktop browser; resulting in companies pivoting their research and funds towards something more elevated, like actually improve their products.
[1]
https://firefox-source-docs.mozilla.org/toolkit/components/telemetry/collection/index.html
[2]
https://pirg.org/edfund/resources/how-mastercard-sells-data/
[3]
https://www.nytimes.com/2018/04/11/technology/facebook-privacy-hearings.html